Anyone who uses the internet–in other words, everyone–needs to understand the concept of Personally Identifiable Information (PII) and the potential risks associated with its exposure or theft.
PII refers to any information that can be used to identify an individual, whether on its own or when combined with other relevant data.
With the increasing reliance on technology in our daily lives, the amount of PII being shared online has grown exponentially, making your data a prime target for cybercriminals.
The exposure or theft of PII can lead to serious consequences, such as identity theft, financial fraud, and reputational damage. Cybercriminals can use stolen PII to gain unauthorized access to bank accounts, apply for credit cards or loans in the your name, or even impersonate you online.
In addition to the personal impact on individuals, PII breaches can also result in significant financial and legal repercussions for organizations entrusted with safeguarding this sensitive information.
Understanding the types of PII, how it can be compromised, and the steps you can take to protect your personal information is essential in in order to stay safe online.
By being aware of the risks and implementing best practices for safeguarding PII, you can reduce the likelihood of falling victim to identity theft or other malicious activities related to the exposure of your personal data.
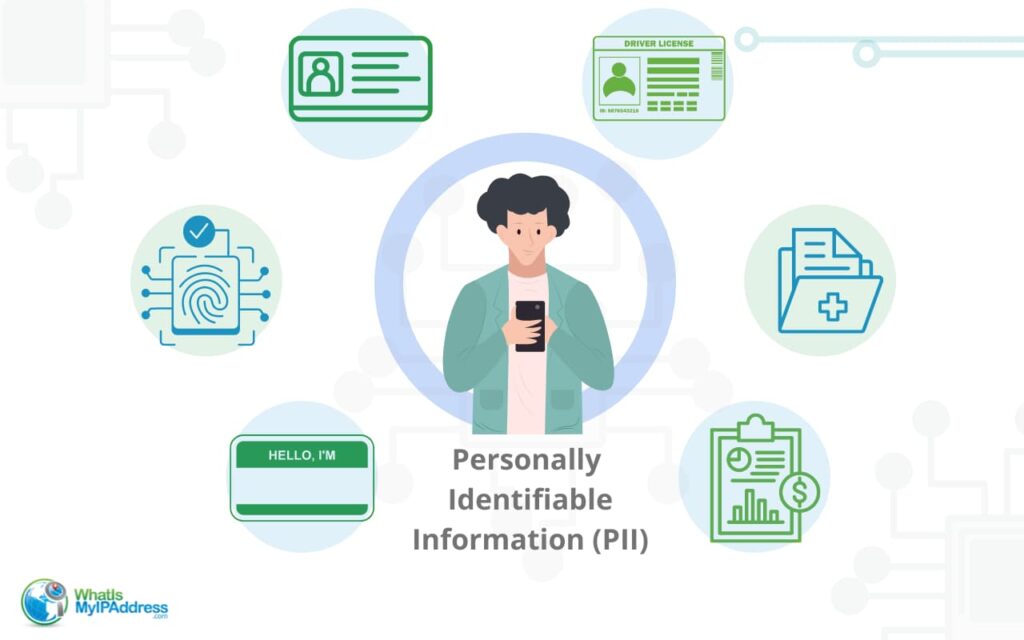
What is Sensitive PII?
Sensitive Personally Identifiable Information is legally identifiable information including a person’s:
- Full, legal name
- Social Security number
- Driver’s license number
- Medical records
- Financial records
- Mailing address
- Credit card number(s)
- Passport number
- Biometric data (e.g., fingerprints, facial recognition data)
- Criminal records
- Genetic information
- Login credentials (usernames and passwords)
These types of PII are considered sensitive because they can be used directly to identify an individual and, if exposed, can lead to serious consequences such as identity theft, financial fraud, or reputational damage.
What is Non-Sensitive PII?
Non-Sensitive Personally Identifiable Information (also called Indirect PII) is information that can be accessed by the general public through sources like websites, corporate directories, phonebooks, and more. This type of PII is not considered sensitive on its own but can still be used to identify an individual when combined with other pieces of information. Examples of non-sensitive PII include:
- Date of birth
- Zip code
- Race
- Religion
- Gender
- Business phone number
- Email address
- Place of employment
- Education information
- Mother’s maiden name
Identifying Individuals with Non-Sensitive PII
While non-sensitive PII may not be as critical as sensitive PII, it can still pose a risk when combined with other pieces of information. These “quasi-identifiers” can be pieced together to create a unique profile of an individual. For example:
- Combining a person’s date of birth, zip code, and gender can narrow down their identity to a small group of people.
- Knowing someone’s place of employment, job title, and email address can make it easier to target them with phishing attempts or social engineering attacks.
- Using a mother’s maiden name, which is a common security question, along with other non-sensitive PII can help attackers gain unauthorized access to accounts.
It’s essential to be aware that even seemingly harmless pieces of information can be used to identify individuals when combined. Protecting both sensitive and non-sensitive PII is crucial in maintaining privacy and security in the digital age.
Data Anonymization Techniques
Data anonymization is the process of modifying or removing personally identifiable information (PII) from a dataset, making it difficult or impossible to trace the data back to a specific individual. The purpose of data anonymization is to protect the privacy of individuals while still allowing organizations to use the data for analysis, research, or other purposes. By anonymizing PII, companies can comply with privacy regulations and reduce the risk of data breaches.
Common data anonymization techniques include:
- Encryption. Encryption involves converting PII into an unreadable format using a special algorithm and a unique key. Only authorized parties with access to the decryption key can view the original data. Encryption is commonly used when storing or transferring sensitive PII, such as financial information or medical records.
- Data Masking. Data masking involves replacing sensitive PII with fictitious but realistic data. This technique maintains the structure and format of the original data while making it impossible to trace back to a specific individual. Data masking is often used when creating test environments or sharing data with third parties for analysis or research purposes.
Other data anonymization techniques include:
- Tokenization: Replacing sensitive PII with a unique, randomly generated token that can be mapped back to the original data when needed.
- Data Perturbation: Adding random noise or slightly modifying the original data values to make it difficult to identify individuals while still maintaining the overall statistical properties of the dataset.
- Data Aggregation: Grouping data into summary categories or ranges, making it harder to identify specific individuals within the aggregated data.
By using these data anonymization techniques, organizations can protect PII while still leveraging the value of their data for various purposes. It’s important to note that no single anonymization method is foolproof, and organizations should carefully consider the specific requirements of their data and the level of protection needed when choosing an anonymization approach.

How to Protect Your Personally Identifiable Information
While it’s difficult to remove all traces of your PII from the internet completely, there are several steps you can take to reduce the amount of personal information available online and minimize the risk of your PII being stolen or misused. Here are some tips to help protect your PII:
- Use strong, unique passwords. One of the most effective ways to protect your PII is to use strong passwords that are unique to each of your online accounts. Avoid using information that’s easily guessable like your birthday or pet’s name, and instead, choose a mix of uppercase and lowercase letters, numbers, and special characters. You might also want to use a password manager to generate and securely store complex passwords.
- Enable two-factor authentication. Two-factor authentication (2FA) adds an extra layer of security to your accounts by requiring a second form of verification, such as a code sent to your phone or generated by an app, in addition to your password. Enable 2FA wherever possible to make it harder for hackers to gain unauthorized access to your accounts.
- Regularly update software and devices. Keep your operating system, web browsers, and other software up to date with the latest security patches and updates. These updates often include fixes for known vulnerabilities that cybercriminals can exploit to steal your PII. Enable automatic updates when possible to ensure you always have the latest security features.
- Be cautious when sharing personal information online. Be mindful of the information you share on social media and other online platforms. Avoid sharing sensitive PII, such as your full address or phone number, and adjust your privacy settings to limit who can see your posts and profile information. Be wary of phishing attempts and unsolicited requests for personal information, as these may be attempts to steal your PII.
- Use privacy-focused services. When browsing the web or using online services, consider using privacy-focused tools like virtual private networks (VPNs) or encrypted messaging apps to protect your PII from being intercepted or monitored by third parties. Look for services that prioritize user privacy and have strong data protection policies in place.
- Personal data removal services. Many individuals are now turning to personal data removal services to safeguard their privacy and protect their personal information. These services systematically erase personal data from online databases, reducing the chances of personal information falling into the wrong hands. This approach not only enhances personal privacy but also provides peace of mind in the face of growing cyber threats.
- Monitor your accounts and credit reports. Regularly check your bank statements, credit card statements, and credit reports for any suspicious activity or unauthorized transactions. If you notice anything unusual, report it to the relevant authorities immediately and take steps to secure your accounts, such as changing your passwords or freezing your credit.
- Dispose of old devices and documents securely. When disposing of old devices or documents containing PII, make sure to properly erase or shred them to prevent your personal information from falling into the wrong hands. Use secure data erasure methods for electronic devices and shred physical documents before disposing of them.
By following these tips and being proactive about protecting your PII, you can significantly reduce the risk of your personal information being stolen or misused by cybercriminals or other malicious actors.
It’s crucial to stay informed about the latest threats to PII and to adopt best practices for protecting your personal information online. By doing so, you can reduce the risk of becoming a victim of identity theft, financial fraud, or other crimes that stem from the misuse of PII.
Your future security depends on today’s actions. Safeguard your PII now to prevent potential threats.